The FTC is pursuing rulemaking around health data security and privacy. Here’s why it matters
The Federal Trade Commission (FTC) recently closed a request for comment on a proposal to modify its Health Breach Notification Rule (HBNR)—which governs how vendors of “personal health records” and entities not covered by the Health Insurance Portability and Accountability Act (HIPAA) handle breaches of health data. Since the rule went into effect in February 2010, the FTC said, changes in the health tech and data landscapes merit a reconsideration of how it should apply. “The proposed amendments to the rule will allow it to keep up with marketplace trends,” said Samuel Levine, director of the FTC’s Bureau of Consumer Protection, “and respond to developments and changes in technology.”
The proposal to update the Health Breach Notification Rule comes as the FTC demonstrates a greater focus on protecting health data privacy. In February 2023, the FTC enforced the rule for the first time ever against prescription drug provider GoodRx—and enforced it again in May against fertility tracking app Premom. Both companies were allegedly violating the rule by sharing individuals’ sensitive health data with third parties, without proper disclosures.
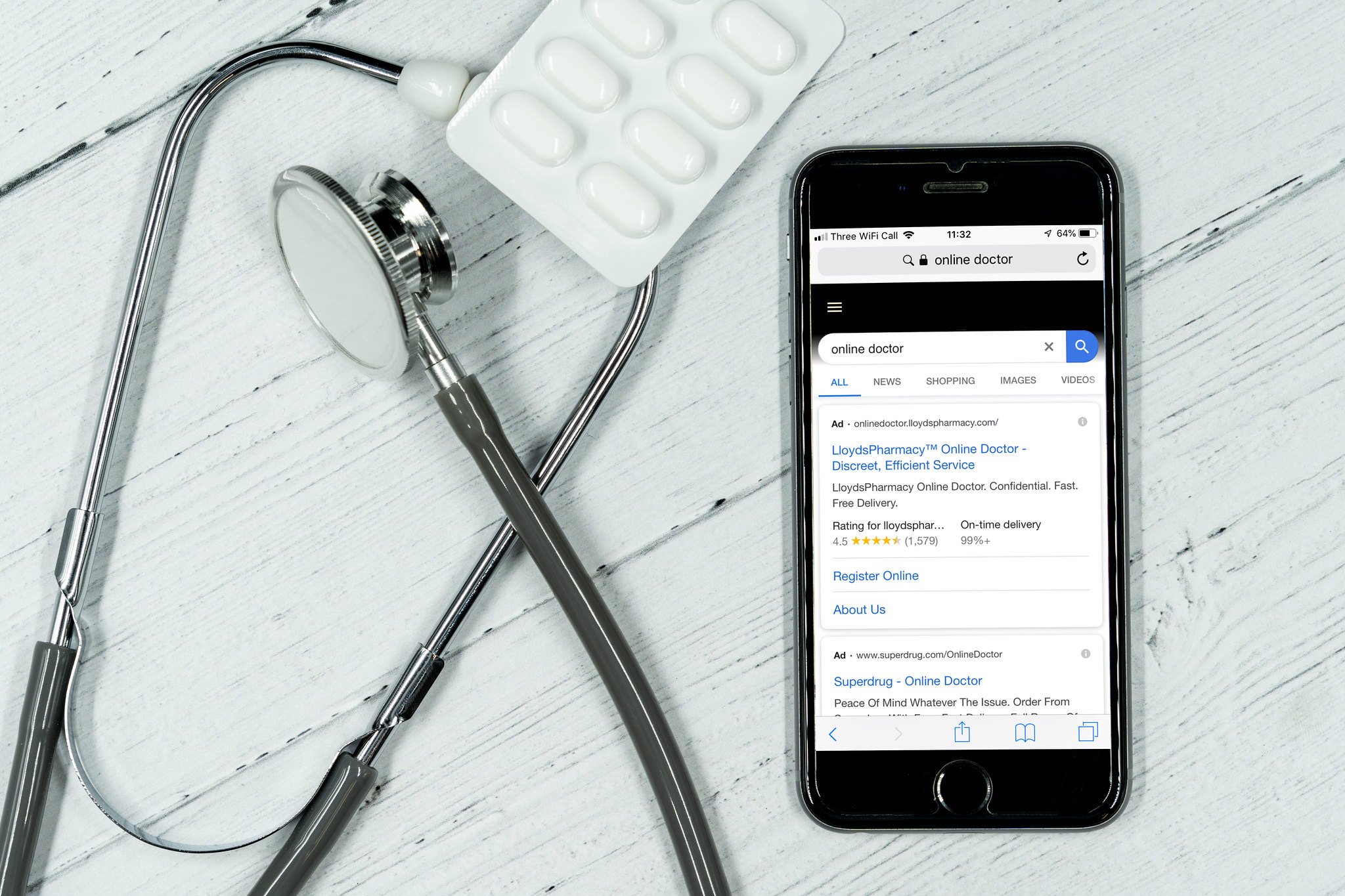
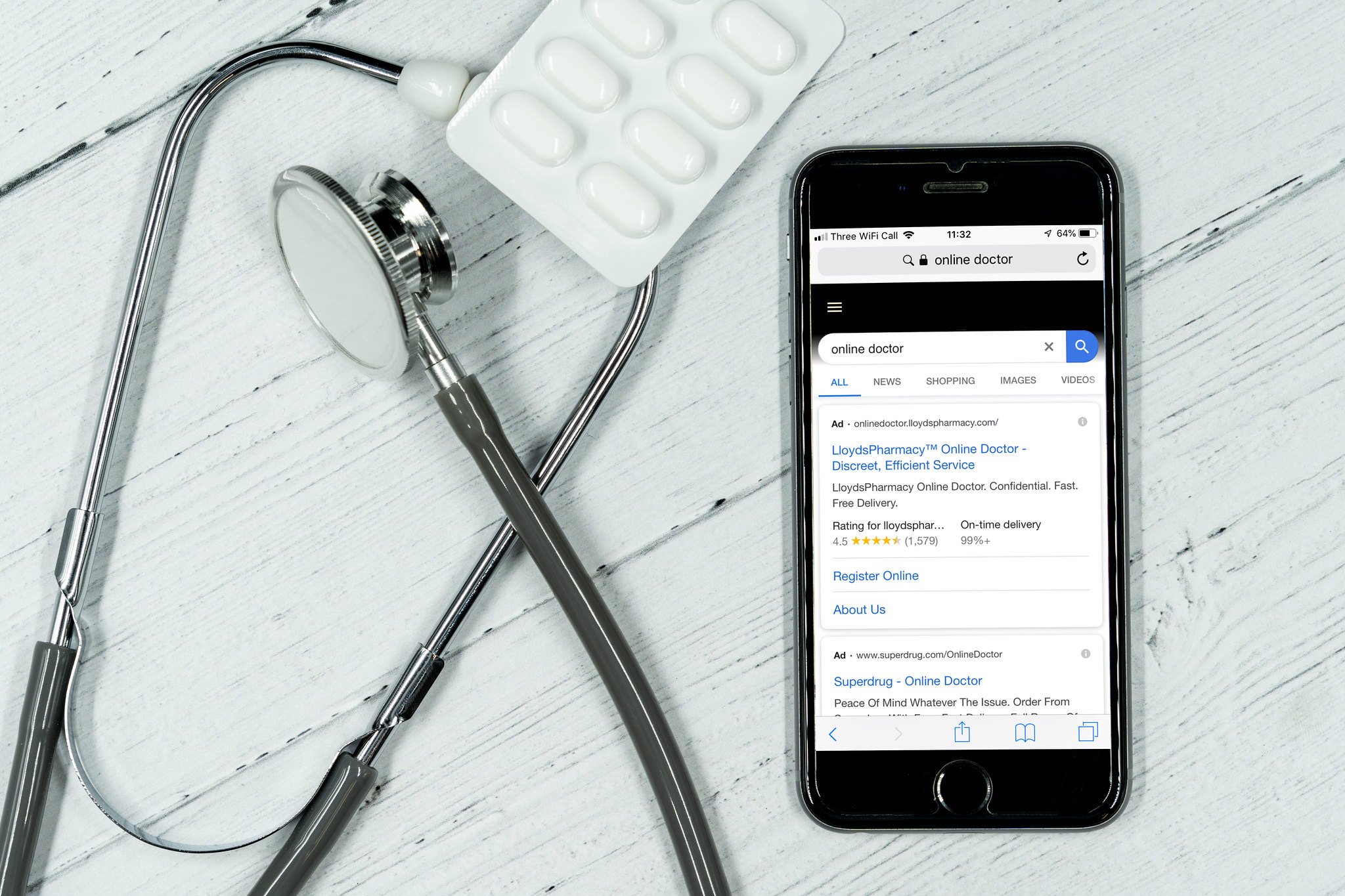
The FTC’s proposal would also update federal health data breach regulations to keep up with significant changes taking place in the health data space, including the expanding role of health tech apps, telehealth services, data brokers, and digital advertisers in collecting, aggregating, identifying, sharing, and selling Americans’ health information. Each of these and other changes will strengthen and clarify how the FTC regulates companies using health data outside the scope of HIPAA.
This article examines the history behind the Health Breach Notification Rule and the FTC’s proposed changes. It then argues that as the FTC considers the public comments it received, it should maintain its proposed expansion of health app coverage, notification requirements, and determination that unauthorized disclosures of health data can constitute a “breach.” The article does not comprehensively cover every element of the proposed rulemaking but suggests that due to gaps in U.S. federal privacy law, the FTC has a considerable opportunity to use its existing legal and regulatory powers to keep pace with health tech developments and appropriately control the ways in which health tech companies, apps, and services gather, transfer, and sell Americans’ health information.
HIPAA and the FTC’s Health Breach Notification Rule
Many health data topics in the United States are intertwined with HIPAA, passed in 1996. HIPAA aimed to streamline health care in the United States through two main objectives: aid the transfer of medical records between places of care and define the term “personal health information” (PHI). Since then, HIPAA has undergone notable changes, namely through the addition of the HIPAA Privacy Rule and the HIPAA Security Rule in the early 2000s (which together established national standards for handling personal health information)—and the passage of the Health Information Technology for Economic and Clinical Health (HITECH) Act in 2009 (which, among other effects, extended the Security Rule to HIPAA-covered business associates). The Department of Health and Human Services is responsible for enforcing HIPAA and its regulations.
However, plenty of companies and other organizations collecting, using, and sharing health data are not covered by HIPAA and its privacy and security rules. HIPAA applies to three main categories of entities: health care providers, health plans, and health care clearinghouses, as well as their business associates. For example, doctors’ offices are covered under HIPAA, and if a doctor’s office hires a third-party company to build its website for patients to book appointments and submit medical symptoms, that company would also be covered as a business associate. But HIPAA does not cover the many social media platforms, advertising technology companies, fertility tracking and reproductive health apps, mental health apps, telehealth platforms, and data brokers outside those three HIPAA categories. Those entities are regulated instead by the FTC.
A decade and a half ago, there was a problem: The FTC had regulatory oversight over many non-HIPAA-covered companies handling health data, but the agency had no specific mandate to address their health privacy practices. Hence, the American Recovery and Reinvestment Act of 2009 required the FTC to issue rules requiring vendors of “personal health records” and related entities to notify consumers when their individually identifiable health information was breached (see Section 13407(b) and Section 13407(g)). The FTC issued a proposal for its Health Breach Notification Rule in April 2009 and implemented the rule in August 2009. It exists alongside the HIPAA privacy regime and deals with non-HIPAA-covered entities—although the FTC noted in its initial 2009 rulemaking that it is possible some organizations are covered by both regimes.
Under the FTC’s rule, personal health record vendors that suffer a data breach must notify individuals in writing of the breach, the personal health information involved, and what mitigation measures have been taken. This includes service providers, which must notify the covered entity of a breach, and the entity then must notify its customers. If a breach affects more than 500 individuals in a particular state or territory or the District of Columbia, the vendor must notify the media as well. In all cases, covered vendors must notify the FTC of breaches.
While the HBNR was revolutionary in advancing patient privacy and health data security, it fell short in a few key areas. The generation, collection, aggregation, and inference of health data has exploded since 2009. In many cases, health technologies have increased health care access and facilitated the easier handling of health records for providers and patients, but these technologies have also exposed private data to a number of harms. Data breaches are becoming more common, and due to the sensitive nature of health records, the health care industry faces a particularly high number of breaches. In the past three years alone, health care data breaches have doubled, according to the Department of Health and Human Services. There has clearly been a need for the FTC and other privacy experts to reevaluate the HBNR in light of these market, technology, and health industry changes. This includes elaborating on the rules to cover more data collection mechanisms (such as mobile apps) and more explicitly articulating guidance for smaller businesses and companies less well versed in privacy and cybersecurity.
The HBNR also originally took the view that data breaches were, generally speaking, hacks of databases—states using exploits to break into servers or cybercriminals sending malware in email attachments that were then opened by unsuspecting employees. This reflects the conventional understanding of a “breach.” Over time, though, as more data are collected about individuals’ health conditions—including from the monitoring of purchases and geolocations—and are gathered and shared by companies, there have been more opportunities to share health data in harmful ways that consumers did not clearly and fully endorse. Many mobile health apps share health information with advertisers, and an entire market exists where data brokers package and sell consumers’ health conditions and other personal data. The FTC’s 2021 policy changes around data sharing further indicated that the original HBNR needs updating for the modern health data landscape.
The FTC’s Proposed Changes to the Rule
The FTC’s proposed changes to the current Health Breach Notification Rule span a number of issue areas. Several of the most significant specific changes fit into three general categories: expanding and clarifying the definition of personal health record identifiable information; formally expanding the definition of a breach to include a company disclosing data without consumers’ authorization; and clarifying how the Health Breach Notification Rule applies to mobile apps and health tech companies. As the FTC processes the feedback received in its request for comment, it should be sure to maintain these modifications it has proposed to ensure the rule better reflects and regulates the current reality of health data collection, processing, transmission, and use. These updates provide important clarity on enforcement measures already taken, emphasize that non-HIPAA-covered health tech companies have regulatory obligations, and fill in gaps that can be plugged while Congress stalls on privacy legislation.
First is the FTC’s expansion and clarification of the definition of covered health data. Currently, the Health Breach Notification Rule classifies “PHR identifiable information” as
“individually identifiable health information,” as defined in section 1171(6) of the Social Security Act (42 U.S.C. 1320d(6)), and, with respect to an individual, information: (1) That is provided by or on behalf of the individual; and (2) That identifies the individual or with respect to which there is a reasonable basis to believe that the information can be used to identify the individual.
The FTC’s proposed modifications would add two more clauses:
-
“relates to the past, present, or future physical or mental health or condition of an individual, the provision of health care to an individual, or the past, present, or future payment for the provision of health care to an individual; and”
-
“is created or received by a health care provider, health plan (as defined in 42 U.S.C. 1320d(5)), employer, or health care clearinghouse (as defined in 42 U.S.C. 1320d(2)).”
Both of these additions would update the rule to reflect how companies predict and otherwise derive health data today—as well as how they acquire health data. The language proposed by the FTC in the first addition quite closely mirrors language in the HIPAA Privacy Rule. It also closely mirrors language used in recent bills and laws around health data, such as the My Health My Data Act in Washington state, signed into law in April 2023, and the Health and Location Data Protection Act of 2022, on which one of us worked, introduced by Sen. Elizabeth Warren (D-Mass.) in June 2022. This first addition is valuable because (a) many companies, including data brokers, combine data sets together and use predictive methods to “infer” data not technically collected, and (b) data that is not technically “health data” under certain laws can in reality reveal health characteristics, such as location data showing a visit to an abortion clinic or payment information revealing a prescription purchase. Broadening the rule’s definition to include provision of health care, payments, future conditions, and other data-generating mechanisms would capture much of this data activity that was previously not covered or questionably covered.
The second proposed addition to “PHR identifiable information” is also important to reflect how the provision of health-care-related services and the processing of health data is relevant not only to HIPAA-covered entities. Health data can originate in multiple places and take multiple forms while still being covered under the HBNR. For instance, a consumer may use an online drug delivery service to receive prescribed antidepressants, and the company could provide that information to an advertiser. Someone seeking treatment for cancer, HIV, or another health condition might visit a specialized facility, and mobile apps on their phone could sell the location pings to a data broker or a health insurance provider. Both of these examples involve consumers engaging in transactions through modern health services, such as using online drug providers, or getting health treatment while being monitored by digital technologies, such as mobile apps. The data in each case could reveal sensitive health information about individuals and be covered under the rule. The addition clarifies that these transactions are unambiguously covered.
The FTC also proposes amending the definition of “breach of security.” As noted above, a breach is a core concept in the HBNR that triggers all kinds of reporting requirements to users and the federal government. It is an important concept for regulatory enforcement. Presently, the HBNR defines a “breach of security” as follows:
with respect to unsecured PHR identifiable health information of an individual in a personal health record, acquisition of such information without the authorization of the individual. Unauthorized acquisition will be presumed to include unauthorized access to unsecured PHR identifiable health information unless the vendor of personal health records, PHR related entity, or third party service provider that experienced the breach has reliable evidence showing that there has not been, or could not reasonably have been, unauthorized acquisition of such information.
To that, the FTC would add:
“A breach of security includes an unauthorized acquisition of unsecured PHR identifiable health information in a personal health record that occurs as a result of a data breach or an unauthorized disclosure.”
The most salient point here is the commission’s explicit shift toward defining unauthorized disclosure as a breach of health data. (Data breaches in the conventional sense—hackers breaking into computer systems—will remain covered under the definition, too.) Unauthorized disclosure, based on this definition (and taking cues from FTC enforcement actions), could include sharing data with advertisers or selling data to data brokers, among other actions. This is not a new idea per se; in the FTC’s September 2021 policy statement on the HBNR, it reminded relevant entities that “[i]ncidents of unauthorized access, including sharing of covered information without an individual’s authorization, triggers notification obligations under the Rule.” In February 2023, the FTC then affirmed this in practice with its first-ever HBNR enforcement action, taken against prescription drug provider and telehealth company GoodRx—which failed to notify consumers of unauthorized disclosures of their data to Facebook, Google, and other companies. It did so again in May 2023 against Premom, a fertility tracking and pregnancy planning app that similarly shared users’ health data without authorization. Hence, the proposed rule change is more of a formal clarification of this policy in definitional form.
Given that the FTC has already made a policy statement and taken enforcement actions in this area, the change is a sensible clarification. Additionally, it is likely useful to many companies not closely following federal privacy regulations. “Breach” taken colloquially could be conceived narrowly as a hacker breaking into a computer system, and noting the other forms a breach of privacy can take is important. Of course, if the rule is changed as indicated, it is an open question whether any company might attempt to challenge this expanded definition of a “breach” in an effort to keep the sharing or selling of consumers’ health data without authorization out of the scope of the HBNR.
Lastly, the FTC’s proposed rule modifications would explicitly clarify how health apps and technologies are regulated. This is, in the FTC’s words, “[t]o ensure that entities covered by the Rule understand their obligations under the Rule.” It adds a new definition for “health care services or supplies,” defined as
any online service, such as a website, mobile application, or internet-connected device that provides mechanisms to track diseases, health conditions, diagnoses or diagnostic testing, treatment, medications, vital signs, symptoms, bodily functions, fitness, fertility, sexual health, sleep, mental health, genetic information, diet, or that provides other health-related services or tools.
Such a definition does not necessarily change how or on whom the FTC will enforce its health privacy regulations. Mobile apps, telehealth services, and other companies involved with digital technologies outside the scope of HIPAA have long been subject to FTC enforcement actions. For clarification purposes, though, this definition makes clear—to many entrepreneurs, developers, and others who may not realize their regulatory obligations vis-a-vis health data—that they are covered under the Health Breach Notification Rule. Whatever their legal or ethical responsibilities, not all companies handling consumers’ health information comprehensively understand (or spend money to understand) their obligations under the HBNR. Hopefully, more explicitly stating some of these shifts in one place, rather than in combinations of documents and enforcement actions, will compel more businesses to increase privacy and security measures around health data.
Looking Forward
The FTC’s health breach rulemaking occurs amid growing attention to health care data breaches, the privacy risks of sharing and selling data, and the increasing use of health tech apps and telehealth services related to the coronavirus pandemic and the U.S.’s ongoing mental health crisis. Simply put, it is a timely, formal proposal to revise years-old health privacy regulations. These changes in many cases serve more as clarifications of existing policies and practice than as major changes to regulatory direction. But they are important nevertheless—especially expanding and clarifying the definition of personal health record identifiable information; formally expanding the definition of a breach to include a company disclosing data without consumers’ authorization; and clarifying how the Health Breach Notification Rule applies to mobile apps and health tech companies.
As these changes are likely rolled out in the coming months, many of them will improve on the privacy regulation status quo. Clarifying definitions will help organizations navigate how health data is shared with third parties and to strengthen protections for high-risk health information (including by aligning definitions with language found in HIPAA and other legislation). As more states follow in Washington’s footsteps to regulate individual health data below the federal level, it will be even more important for companies and organizations to understand their regulatory obligations—and for regulators such as the FTC to weigh how these different laws and regulations impact the landscape of harmful health practices, such as selling highly sensitive health data without consumers’ consent.
In enforcing the Health Breach Notification Rule twice this year, the FTC has shown that it is not afraid to exercise its regulatory power when illegal and harmful uses of consumers’ health data take place. This could include everything from a non-HIPAA-covered telehealth company selling data in violation of the company’s own privacy policy to a mobile mental health app using data in ways that cause substantial, unavoidable injury to consumers. Health technologies continue to evolve rapidly, and formal revisions to the Health Breach Notification Rule are long overdue. As Congress continues to stall in passing comprehensive privacy legislation, the FTC’s rule update will help to address some harms in the meantime under the power of existing laws.
– Justin Sherman, Devan Desai, published courtesy of Lawfare.